Top Cyber Attacks of August 2022
Our 24x7x365 security operations team closely monitors all cyber news and related cyber attacks through our own insider sources to ensure our customers Get There First™- every time. Here are our SOC's top cyber attack picks from August 2022:
Ransomware Attack Shuts Down 175 Denmark 7-Eleven Stores

7-Eleven stores in Denmark suffered a ransomware cyberattack in early August, quickly shutting down 175 locations' point of sale (POS) retail payment systems. Jesper Ostergaard, CEO of 7-Eleven Denmark, told a local TV station that the first indication that the chain had been targeted by hackers came when one register staff member reported that they were unable to process payments. The company did not provide any info on the gang responsible other than confirming that threat actors breached their network and encrypted systems.
Industry: Retail-Convenience
Key takeaway: It is critically important that your network is properly segmented so that you can carefully filter and limit internet access to operational networks, identify links between these networks, and develop workarounds or manual controls to ensure ICS networks can be isolated if your corporate network is compromised.
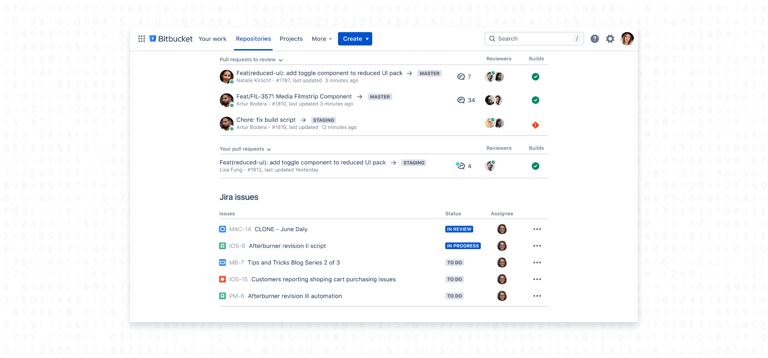
Critical Hole in Atlassian Bitbucket Allows any Miscreant to Hijack Servers
A critical command-injection vulnerability in multiple API endpoints of Atlassian Bitbucket Server and Data Center was discovered, allowing an unauthorized attacker to remotely execute malware, and view, change, and even delete data stored in repositories. This latest bug follows a series of hits for the enterprise collaboration software maker. While Atlassian has fixed the security holes present in versions 7.0.0 to 8.3.0, the Center for Internet Security has labeled this vulnerability as high for businesses and government entities of all sizes.
CVE ID: CVE-2022-36804
CVSS score: 9.9/10🔥
Industry: Software
Key takeaway: While we have not seen reports of active exploitation, this critical vulnerability will be enticing to cybercriminals who will look to exploit victims who have not patched. Atlassian recommended organizations upgrade their instances to a fixed version, and urged those with configured Bitbucket Mesh nodes to update, too.
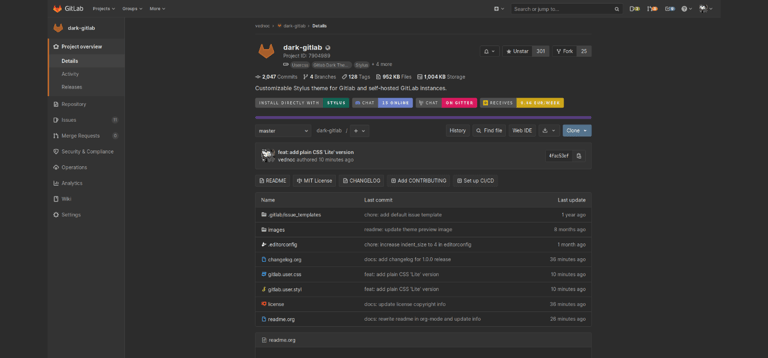
GitLab Patches Critical Remote Code Execution (RCE) Vulnerability
DevOps platform, GitLab, issued patches for a critical remote code execution (RCE) vulnerability impacting its GitLab Community Edition (CE) and Enterprise Edition (EE) releases. Affecting all versions starting from 11.3.4 before 15.1.5, all versions starting from 15.2 before 15.2.3, and all versions starting from 15.3 before 15.3.1, the vulnerability allowed an authenticated user to achieve remote code execution via the Import from GitHub API endpoint.
CVE ID: CVE-2022-22047
CVSS score: 9.9/10🔥
Industry: Internet Hosting Service for Software Development
Key takeaway: Using this vulnerability, a threat actor could've taken control over the server, steal or delete source code, perform malicious commits, and more. While GitLab has not mentioned any active exploitation attempts of CVE-2022-2884 in the wild, users should've updated to the latest versions of CE/EE. If updating was not feasible, GitLab recommended disabling the import function altogether.
LastPass Developer Systems Hacked to Steal Source Code
Popular password management company, LastPass, suffered a breach enabling threat actors to exfiltrate the company's source code and proprietary technical information. Sources reported that LastPass employees were scrambling to contain the attack after the discovery and confirmation of the breach. While LastPass reports that there was no evidence that customer data or encrypted password vaults were compromised, the threat actors did steal portions of their source code and "proprietary LastPass technical information."
Industry: Information Technology and Services
Key takeaway: With over 33 million people and 100,000 businesses using LastPass' software to safely store their passwords, this attack could've had irrefutable damage This attack validates why all users should enable multi-factor authentication on their LastPass accounts. In the event that threat actors compromise your password, having an additional layer of security will prove beneficial in stopping the attackers from accessing your account.
Slack Admits to Leaking Hashed Passwords for Five Years
Popular collaboration tool, Slack, used by more than 100,000 global organizations and 10,000,000 users, revealed that one of their low-friction features had inadvertently been oversharing personal data whenever users created or revoked a shared invitation link for their Slack workspace. Slack shared that the data sent to the recipients of such invitations included the sender’s hashed password. Slack’s security advisory doesn’t explain the breach very clearly, saying merely that “[t]his hashed password was not visible to any Slack clients; discovering it required actively monitoring encrypted network traffic coming from Slack’s servers.”
Industry: Software
Key takeaway: Though Slack reported that it was unlikely that the content of passwords were compromised as a result of the flaw, they forced password resets on roughly 1 in 200 (0.5%) of their users confirmed to be affected by this discovery. Users should store their passwords on a secure password manager and enable 2FA functional capabilities so that each time their logging in, they're not only entering their password, but also a randomized on-time code that changes each and every time. This added layer of protection ensures that even if your password is revealed, it's not enough on its own to takeover your personal accounts.
About Digital Hands
As a new kind of MSSP, Digital Hands is how organizations are getting ahead of the bad guys in a world where compliance alone is no guarantee of protection. Too many companies invest in cybersecurity solutions, follow the recommendations, achieve compliance … and then still get breached. You’ve got to get to your exposures before the bad guys do.
To help you do just that, we've outlined the most common types of threat actors, how they impact you, and controls you can implement to ensure you get ahead of every threat in our latest guide!